Pentest Chronicles
Credentials Exposure In Tinycontrol Devices

Paweł Różański
March 23, 2026
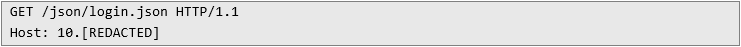
We decided to check if there is a possibility to perform command injection or read sensitive files. Instead, I found something more interesting: during the opening of the login page by an unauthorized user, the file login.json was fetched from the device.
Request:
 Response:
Response:
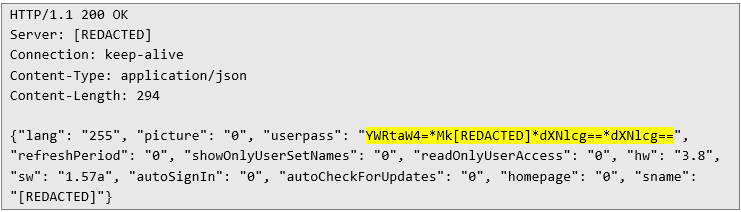 The userpass field was very interesting, I was immediately struck by familiar base64 strings. It turned out that it contains base64 encoded usernames and passwords, encoded with base64 and separated by asterisk.
Impact
What is the impact? In the worst-case scenario remote, unauthenticated attacker can log in as an administrator, no matter how complicated the password is. Later, after contact with the vendor, it turned out that if recommended configuration is applied instead of default one, attacker may need initial access to the device as a user (need to know user password), so it is “barely” privilege escalation.
The userpass field was very interesting, I was immediately struck by familiar base64 strings. It turned out that it contains base64 encoded usernames and passwords, encoded with base64 and separated by asterisk.
Impact
What is the impact? In the worst-case scenario remote, unauthenticated attacker can log in as an administrator, no matter how complicated the password is. Later, after contact with the vendor, it turned out that if recommended configuration is applied instead of default one, attacker may need initial access to the device as a user (need to know user password), so it is “barely” privilege escalation.
Quickly checked release notes, found no signs of fixing this issue, so after informing our customer about security finding in the tested network – decided to contact the vendor. With the help of CERT Polska, CVE-2025-1150 was published. Timeline 29.07.2025 – Initial contact with the vendor.
21.08.2025 – Full details sent to the vendor.
16.03.2026 – CVE published.
Next Pentest Chronicles
When Usernames Become Passwords: A Real-World Case Study of Weak Password Practices
Michał WNękowicz
9 June 2023
In today's world, ensuring the security of our accounts is more crucial than ever. Just as keys protect the doors to our homes, passwords serve as the first line of defense for our data and assets. It's easy to assume that technical individuals, such as developers and IT professionals, always use strong, unique passwords to keep ...
SOCMINT – or rather OSINT of social media
Tomasz Turba
October 15 2022
SOCMINT is the process of gathering and analyzing the information collected from various social networks, channels and communication groups in order to track down an object, gather as much partial data as possible, and potentially to understand its operation. All this in order to analyze the collected information and to achieve that goal by making …

PyScript – or rather Python in your browser + what can be done with it?
michał bentkowski
10 september 2022
PyScript – or rather Python in your browser + what can be done with it? A few days ago, the Anaconda project announced the PyScript framework, which allows Python code to be executed directly in the browser. Additionally, it also covers its integration with HTML and JS code. An execution of the Python code in …


