
Pentest Chronicles
A small oversight with big consequences: how a minor mistake can lead to the compromise of your Domain Controller.
Dominik Antończak
4 August 2023
Have you ever wondered how much information you can glean about others through observation? In the real world, when we're in public places, we're not always conscious of who's watching us and what information they're gathering about us.
We often think we live in a good world, where evil is far from us, but the reality is quite different, and this also applies to the digital world. Some users, just like in everyday life, believe that no one is observing us on the Internet. Nothing could be further from the truth.
Active Directory is a perfect comparison here. At first glance, everything seems invisible; administrators seem to have complete control and their major security mistakes remain unseen by employees. Sometimes, things are put in place temporarily, but this temporary period becomes a year, two, or even a decade, waiting for someone to discover them.
This was exactly the case here. It took 7 years for this minor mistake or oversight to be detected. It all started during an audit. A bit of luck at the very beginning resulted in the first results being a group of users with a strange value written in the description field. A quick verification only confirmed my suspicions - it's the user's password! The question immediately arises - who are these users? Is one of them part of a privileged group? Maybe one of them has access to the domain controller or other systems/users that can be used to gain access to the domain?
I began to verify the users' group memberships. The first two, nothing interesting according to privileges. I didn't lose hope and continued the analysis; I still had three accounts to check. The third user is part of the "Domain Admins" group:
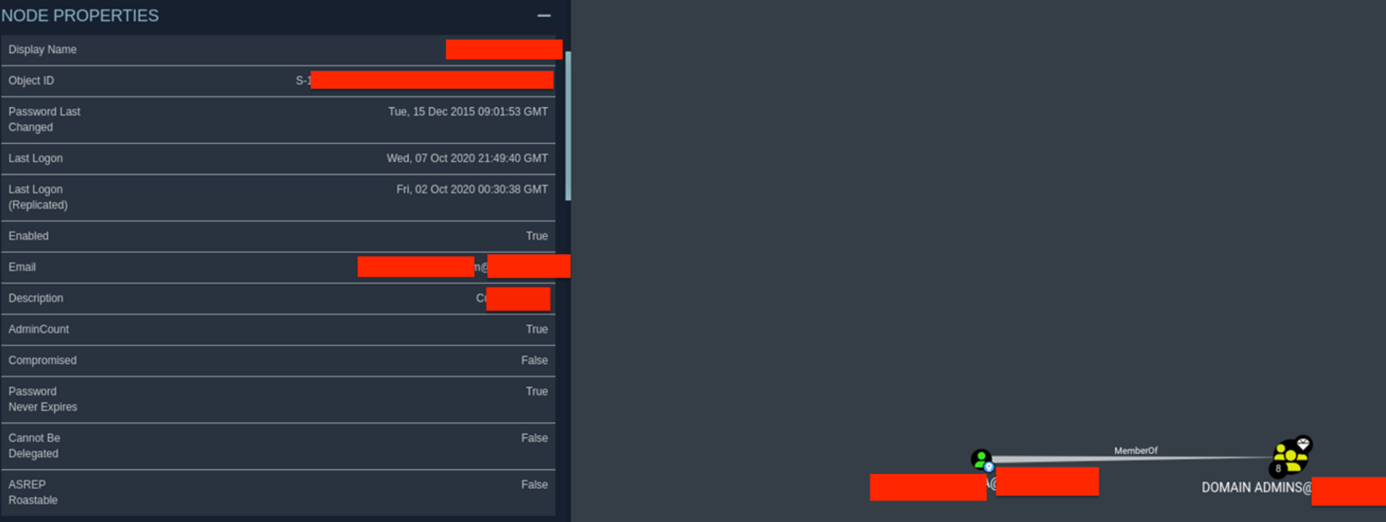
At first glance, the situation is as follows: the password was last changed in 2015, the last login was in 2020. So now, the most important part, what is the status of this account?
Enabled. BINGO!
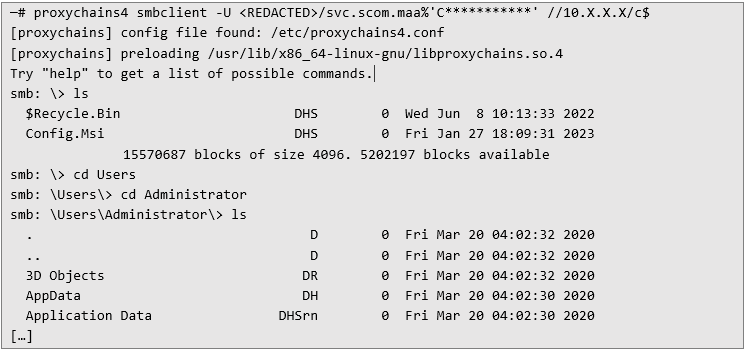
Now all that's left is to break into the domain controller and voilà:
Since this was just a pentest, theoretically, this is where further attacking the infrastructure would stop. However, it's worth doing a dump of the NTDS.DIT and SAM databases to perform a brute force attack to verify employee passwords.
And here's a small bonus 😉
The brute force attack performed later resulted in cracking more than 1000 unique passwords out of about 4000 available (31.26%), granting access to 1800 accounts. Yes, passwords were often repeated among users, there were, of course, classics like Spring2023 or 12345678.
Mission success!
As you can see, what seemed like a small, invisible mistake to most led to the takeover of the domain controller and the cracking 31.26% of passwords.
It's important to remember that virtually all attributes assigned to users are visible to even the least privileged user in AD, so care must be taken not to store sensitive and confidential information in them. The attacker, like a predator, always has his eyes wide open and doesn't always have to use exploits to achieve his goal.
Furthermore, it's crucial to implement a strong password policy. The simplest and best to implement (for users) would be to use passwords made up of several words, containing numbers and special characters, for example:
Green-Red-Elephant-33!
The password doesn't make sense, but it's strong and easy to remember, which is precisely the point.
#Cybersecurity #ActiveDirectory #DomainController #PasswordPolicy #InfoSec
Next Pentest Chronicles
When Usernames Become Passwords: A Real-World Case Study of Weak Password Practices
Michał WNękowicz
9 June 2023
In today's world, ensuring the security of our accounts is more crucial than ever. Just as keys protect the doors to our homes, passwords serve as the first line of defense for our data and assets. It's easy to assume that technical individuals, such as developers and IT professionals, always use strong, unique passwords to keep ...
SOCMINT – or rather OSINT of social media
Tomasz Turba
October 15 2022
SOCMINT is the process of gathering and analyzing the information collected from various social networks, channels and communication groups in order to track down an object, gather as much partial data as possible, and potentially to understand its operation. All this in order to analyze the collected information and to achieve that goal by making …

PyScript – or rather Python in your browser + what can be done with it?
michał bentkowski
10 september 2022
PyScript – or rather Python in your browser + what can be done with it? A few days ago, the Anaconda project announced the PyScript framework, which allows Python code to be executed directly in the browser. Additionally, it also covers its integration with HTML and JS code. An execution of the Python code in …


