Description
It seemed to be a usual LAN test, but the network contained some non-typical devices. One of them was an IoT device (LAN controller), which looked interesting. It had separate admin and user accounts. The user had only read-only permissions, but a default password. The password for the admin was changed from the default one.
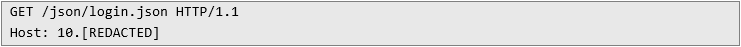
We decided to check if there is a possibility to perform command injection or read sensitive files. Instead, I found something more interesting: during the opening of the login page by an unauthorized user, the file login.json was fetched from the device.
Request:
Response:
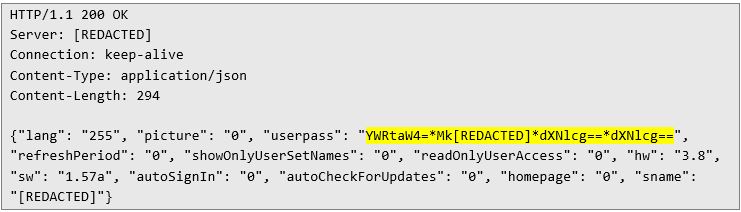
The userpass field was very interesting, I was immediately struck by familiar base64 strings. It turned out that it contains base64 encoded usernames and passwords, encoded with base64 and separated by asterisk.
Impact
What is the impact? In the worst-case scenario remote, unauthenticated attacker can log in as an administrator, no matter how complicated the password is. Later, after contact with the vendor, it turned out that if recommended configuration is applied instead of default one, attacker may need initial access to the device as a user (need to know user password), so it is “barely” privilege escalation.
Quickly checked release notes, found no signs of fixing this issue, so after informing our customer about security finding in the tested network – decided to contact the vendor. With the help of CERT Polska, CVE-2025-1150 was published.
Timeline
29.07.2025 – Initial contact with the vendor.
21.08.2025 – Full details sent to the vendor.
16.03.2026 – CVE published.